READ TIME: 5 MIN

The Difference Between IT & “Almost” IT
What is IT and “Almost” IT? Well, IT is a Managed Service Provider (MSP), that employs hundreds of tenured IT experts available 24/7/365. “Almost” IT are 10 IT professionals in a 20-person company with 200 customers. Think Amazon versus a local delivery service: one has a multitude of staff, resources, and partnerships to deliver purchases the next day—or even the same day—across the country, and the other is a kind of local mom-and-pop service that has limited resources and takes a week to distribute packages two towns over.
If you think that “Almost” IT gives you the most bang for your buck, read on as we’ve broken down the differences between IT and “Almost” IT in a few light-hearted memes that could prove beneficial to your business’ IT strategy.
You’re welcome.
IT
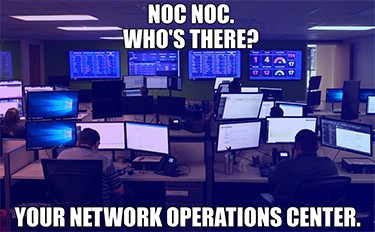
An MSP’s Network Operations Center, or NOC, hosts a team of skilled IT professionals who work in shifts throughout the day, addressing tickets and IT concerns, monitoring systems, updating with security patches, and ensuring clients experience optimal IT performance. MSPs usually have not one but multiple NOCs in different locations. Think Marvel Avengers-style command centers on Helicarriers.
VS
Almost IT

A group of 10 or even 20 IT consultants may sound sufficient for your business’ needs…but physical limitations, including time and resources, adversely affect their bandwidth and capability to address your employees’ needs and resolve crises in a timely manner. Tickets can pile up quickly. “Almost” IT is kind of like Peter Parker running around in a ski mask before Tony Stark gave him the high-tech suit that made him both more capable and more efficient in helping the neighborhood.
IT

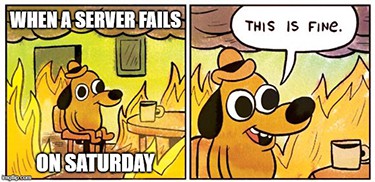
If there’s something strange in your network system at 2 a.m. Tuesday or 2 p.m. Saturday, who are you going to call? Your MSP. The NOC is a 24-hour, 7-days-a-week, 365-days-a-year beehive on a caffeine craze. They are there for you whenever you need them. Even if a blizzard in Texas knocks out a NOC, there’s another in Colorado ready to help.
VS
Almost IT

Everyone has to sleep, including the “almost” IT team that operates on normal business hours. Even if the 10 IT professionals put in the extra effort and stay up all night fixing your system, they won’t be efficient—or awake—the next day. Also, don’t mess with their weekends. Trust me, they’re not answering your Saturday call even with their phones clamped in their hands.
IT
Being proactive is an essential IT strategy, which an MSP is all about. Their team of IT experts will not only install antivirus software and firewalls, but also audit your systems for risks, patch up weaknesses, and monitor your systems via their 24-hour Security Operations Center (SOC). An MSP can also implement data backup and disaster recovery services to ensure business continuity in case of a loss. Security does not sleep, and the SOC is ever watchful.
VS
Almost IT

Loaded down with tickets in a 9 to 5 setting, an “almost” IT business tends to be reactive, only having the bandwidth to respond to events rather than working ahead of time to prevent them; kind of like finding out your smoke detectors don’t work when you really need them instead of testing them every month. Antivirus software and firewalls are not enough. It takes a large team to effectively monitor systems 24/7. Also, what if your system is hacked the one week their lone cybersecurity expert is on vacation? Gulp!
IT
Innovation is one of an MSP’s greatest strengths. The size and experience of the organization allows the MSP to stay ahead of the digital curve. It acquires the latest technologies to keep its clients productive and secure and updates systems and processes to help businesses meet changing compliance standards.
VS
Almost IT
Your “almost” IT provider may still be putting out the fires from the weekend and digging themselves out of tickets. Their small business cannot invest time and finances into new equipment and systems as often as an MSP or hire as many IT specialists with varied backgrounds and expertise as an MSP. Let’s face it: They won’t mention the new standards unless you do.
IT
An MSP thrives or dives by their customers. If a client isn’t happy, an online review or verbal testimonial can damage an organization’s reputation. That’s why an MSP is committed to providing their clients superior customer service. A hundred live help desk and client care representatives are trained on the optimal protocols for various IT incidents and equipped with top-notch tools and IT specialists to efficiently resolve issues 24 hours a day. Basically, they close tickets like Yoda closes duels.
VS
Almost IT
The problem with hiring your friend’s small IT business to manage your company’s IT systems is the familiarity. The very thing that was supposed to make the business alliance easier is the very thing that makes it that much harder. Have you ever tried to tell your friend they’re overcharging you? Or they’re listening but not really hearing you? Or that their one customer service representative had you on hold for an hour on Friday and since they didn’t get to it then, you request the security breach be fixed over the weekend? But it is their cousin’s best friend’s baby’s 1st birthday party! Oh, and you’re invited. Don’t forget a gift!
IT

Who doesn’t love predictable spending for reliable budgeting? A fixed monthly fee ensures that your business will receive the utmost care and end user experience, all for a consistent sum, even if there is an incident like a downed server. That kind of cost savings is something to shout about.
VS
Almost IT

Unpredictable costs are no laughing matter. If a server goes down, your “almost” IT provider will charge your company for extra hours and maybe even overtime if they work outside the normal business hours. That bill will throw your budget for the month out the window. And that makes Leo snicker.
Now that you know the distinctions between IT and “Almost” IT: Who would you rather have maintaining your business’ IT infrastructure, supporting your employees’ IT needs, and securing your sensitive data?
As an award-winning MSP, NexusTek strives to help your business’ IT infrastructure and operations thrive, even if it is just enlightening you with IT-related memes. As a true IT provider, NexusTek’s 300 staff and 24-hour NOCs and SOCs can help your business step up its managed IT and cybersecurity game and balance its monthly budget, all while delivering a local and dedicated customer experience.

We welcome you to join NexusTek, a true IT provider that focuses on the customer experience.